SQL injection used to be a widely used hacking technique to manipulate the WordPress database. Nowadays, Cross Site Scripting (XSS) is popular and has become the number one method to hack a WordPress site.
In this guide, I will be covering the basics of WordPress SQL Injection and how one can get rid of it. In the next part, I will be covering Cross Site Scripting. Let’s get started!
- What Is SQL Injection?
- Entry Points for SQL Injection Attacks
- Why Are SQL Injection Attacks Common?
- How SQL Injection Works?
- Ways to Prevent SQL Injection in WordPress
- Tip#1 Scan for SQL Injection Vulnerabilities
- Tip#2 Update, Update, Update!
- Tip#3 WordPress Theme & Plugins
- Tip#4 Use Trusted Form Plugins
- Tip#5 Hide WordPress Version
- Tip#6 Change Database Prefix
- Tip#7 Always Take a Backups
Tip#8 Keep Logs - Tip#9 Use a Firewall
- Tip#10 Remove Unnecessary Database Functionality
- Frequently Ask Questions
- Final Words!
What Is SQL Injection?
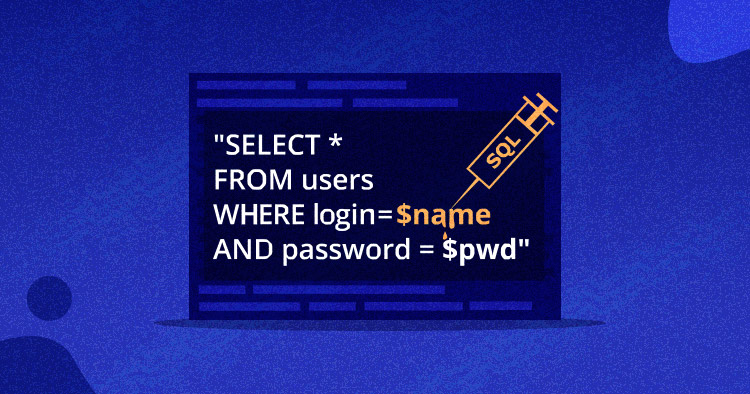
SQL Injection is the result of loopholes in the backend coding. An attacker can easily abuse the input fields by inserting malicious code that could execute SQL commands and can create, retrieve, update, and even delete the data in the database.
SQL is the short-form for Structured Query Language — the most widely used language for the database in web development. Here are the few most popular database engines that use SQL.
Databases Using SQL
We have a lot of database software available in the market. The popular ones include:
- Oracle
- MySQL
- SQL Server
- PostgreSQL
- MongoDB, etc.
As you can see, MySQL is the second in the list. WordPress that uses SQL alone has contributed to more than 35% of WWW and has become the most attractive target for attackers.

Entry Points for SQL Injection Attacks
All input fields are considered as the most common entry points for SQL Injection attacks. In Layman’s term, we can say:
- Sign up forms
- Login forms
- Contact forms
- Site searches
- Feedback fields
- Shopping carts
Why Are SQL Injection Attacks Common?
There can be multiple reasons for this, but, here are the most common that I recall while writing the guide.
- Most of websites database are based on SQL
- WordPress – the most widely used CMS uses SQL for database
- Nearly all websites have input fields to collect information from their visitors
- All websites have at least one of the SQL Injection entry points
- SQL Injection scanning tools are readily available online
- It does not require any technical complexity to exploit
Don’t wait until it’s too late. Take Action Now!
Prevent SQL injection attacks on your website with the Cloudflare Enterprise add-on!
Automate website security with Cloudflares managed Web Application firewall & DDoS mitigation at layers 3, 4, & 7!
How SQL Injection Works?
For instance, you have a contact us form where one needs to enter a phone number. There should be certain criteria like one should enter the limited numbers only with a proper format.
Most of the developers that do not know the input validations might set this field as the plain text meaning one can enter any string that can be the malicious code too. By using some altered SQL queries, one can request the admin username and password.
WordPress SQL Injection Examples
You can find a lot of SQL Injection vulnerabilities with a simple Google search. But, today, let me share a real-life example: one need only look to the gaming industry. As it happens, many SQL injection attacks focus on video games, one of the largest and most profitable industries around.
Besides, in the past hackers also attacked individual websites either blogs, eCommerce stores,s and some of the largest businesses.
It’s happening for a long time, another example of vulnerability in WordPress reported back in Sep 2017. WordPress Core was not directly affected by this vulnerability, however, a patch (WordPress 4.8.3) was released to prevent it from affecting WordPress plugins and themes.
Anthony Ferrara, the man behind the above vulnerability, wrote an extensive guide on WPBD SQL Injection, how it can affect a WordPress site and the precautions to every WordPress user.
There is no foolproof way to secure a WordPress site. In fact, even the WordPress security plugin was affected in the past. In 2014, one of the most popular security plugins demonstrated TWO vulnerabilities that allowed for SQL injection.
Ways to Prevent SQL Injection in WordPress
Being an open-source platform, WordPress sites remain vulnerable to constant hacking attempts, which are hard to control. However, we can take proactive measures to minimize the risks of security threats. Most importantly, you must choose secure WordPress hosting to protect your site against malicious attacks.
Once you’ve chosen a suitable host, you can use the following techniques to prevent SQL injection in your WordPress site.
Looking for better performance and security?
Migrate your WooCommerce website to Cloudways at zero cost.
Tip#1 Scan for SQL Injection Vulnerabilities
You can find a number of online tools to scan your WordPress site. I have shortlisted the top-rated where all you need to do is just enter the WordPress site URL and start scanning for discovered vulnerabilities.
- WordPress Security Scan – Checks for basic vulnerabilities on your WordPress site. Advanced scans are available with a premium upgrade.
- Sucuri SiteCheck – Your WordPress site can be checked for known malware, blacklisting status, errors, and if your site is out-of-date.
- WPScan – A self-hosted vulnerability scanner that is free for personal use. You can also get a paid license for commercial use.
By running a scan report, you can see exactly which areas need to be focused to improve WordPress security.
Tip#2 Update, Update, Update!
The most important for every WordPress user! Keep everything updated including WordPress core, theme, and plugins.
WordPress Core
According to the official WordPress stats, only 29.3% of WordPress sites are using the latest version (5.5.x). All previous versions can be vulnerable and might result in getting hacked. In the above example of SQL Injection vulnerability, you see, all the sites that are below the latest version are vulnerable to the discovered vulnerability. If your site got hacked, I hope you know who will be responsible!

PHP Versions
PHP, the backend of WordPress has been improved a lot over the last few years. A lot of patches and performance-oriented changes have been made. But still, more than 23% of WordPress users are using PHP 7.2 that can be one of the factors for SQL Injection in WordPress. The latest version of PHP is 7.4
Note: If your WordPress hosting does not support the latest versions of PHP, it’s time to switch the host immediately to a managed WordPress hosting that supports the latest versions of PHP like Cloudways.

Tip#3 WordPress Theme & Plugins
Most of the vulnerabilities including SQL Injection in WordPress were discovered in the plugins and themes, not the WordPress core. Keep an eye on the updates, fixes, and adapt accordingly.
If a theme and plugin are not updated regularly, that can be a question mark on your WordPress site. Always use a theme/plugin that updates frequently.
Note: Before performing an update, check the compatibility between the WordPress core, themes, and plugins to make sure your site is working as it should be. To test, you can make a copy of your live website, and then check the compatibility in the WordPress staging environment.
Tip#4 Use Trusted Form Plugins
If you run a business or even a simple blog, you must know the importance of forms like registration forms, login forms, contact forms, etc. With a number of plugins available in the WordPress repository, it’s hard to find the best one. Therefore, to narrow down your search, we have compiled a list of best WordPress Form plugins.
Note: Don’t forget to check out the previously discovered vulnerabilities and its resolution before choosing any plugin.
Tip#5 Hide WordPress Version
It is always suggested not to display the WordPress version publicly. Having this information publicly available can make the way easier for attackers to exploit known vulnerabilities on a particular version.
To hide the WordPress version, just copy and paste below the line of code into the functions.php file of your active theme.
remove_action(‘wp_head’, ‘wp_generator’);
Tip#6 Change Database Prefix
When you install WordPress, by default, the database prefix sets to “wp_”. Most of the WordPress users ignore and just install with the default settings. Guessing the database tables become easier to exploit using SQL Injection techniques.
Do not worry, if you already have WordPress installed. There is an excellent guide on how you can change database prefix in WordPress.
Tip#7 Always Take a Backups
Backups may not be directly related to SQL Injection. But, it can help you to recover a hacked site. WordPress backups can be stored in two ways:
- Local Backup: The backup that is generated automatically and/or manually and is located on your hosting provider. It is not suggested to keep a local backup if you are with shared hosting, once a server is compromised you may also lose the backups. However, if your server is in good hands like Cloudways, then you can keep local backups for WordPress.
- Offsite Backup: Automated and/or manual backups will be generated and sent to the desired off-site storage location like Google Drive, Dropbox, Amazon S3, etc. We have written an extensive guide to back up WordPress sites.
Tip#8 Keep Logs
Dre Armeda, the co-founder of Sucuri once said:
People Are And Will Continue To Be The Biggest Security Issue With WordPress.
Meaning, you have to do your share. Keep an eye on the changes and you should keep a log of everything that is happening on your WordPress site. It will help you to track the changes done by You and/or an attacker so that you can act accordingly.
There is an excellent WordPress security audit log plugin that will surely help you out! Additionally, your hosting provider also keeps logs of everything. Keep reading the logs occasionally.
Tip#9 Use a Firewall
One of the best and important things is to use a firewall that ensures that customer data is safe and protected. In addition to this, you can also define the level of access users based on different factors such as the subscribed package. If you are using Cloudways then you don’t need to worry about it. All Cloudways hosted servers are protected by OS-level firewalls that filter out malicious traffic and keep out the intruders.
Tip#10 Remove Unnecessary Database Functionality
One of the most effective techniques to remove database unnecessary database functionality and content. The more vulnerable it is to a potential SQL injection attack. To prevent this, normalize your database and make your site better and smarter.
Frequently Ask Questions
Q: What Is SQL Injection?
A: SQL Injection is the result of loopholes in the backend coding. An attacker can easily abuse the input fields by inserting malicious code that could execute SQL commands and can create, retrieve, update, and even delete the data in the database.
Q: What is the WordPress SQL injection example?
A: It’s happening for a long time, another example of vulnerability in WordPress reported back in Sep 2017. WordPress Core was not directly affected by this vulnerability, however, a patch (WordPress 4.8.3) was released to prevent it from affecting WordPress plugins and themes.
Q: What does a SQL injection do?
A: SQL Injection was the most basic and widely used hacking technique to manipulate the WordPress database. Nowadays, Cross Site Scripting (XSS) is popular and has become the number one method to hack a WordPress site.
Final Words!
As said earlier, there is no foolproof way to protect a WordPress site. There is always a possibility to get hacked, this can be because of the vulnerability in the core, theme, and plugins. That’s why it is always suggested to be UPDATED! SQL Injection has been controlled a lot in the last few years.
If you ever faced any kind of WordPress SQL Injection attack, share your experience and also how you get rid of it. I’m sure it would help other WordPress users.
Abdul Rehman
Abdul is a tech-savvy, coffee-fueled, and creatively driven marketer who loves keeping up with the latest software updates and tech gadgets. He's also a skilled technical writer who can explain complex concepts simply for a broad audience. Abdul enjoys sharing his knowledge of the Cloud industry through user manuals, documentation, and blog posts.


